Infrastructure That Never Goes Down
GuardianMesh provides distributed relay infrastructure with cryptographic identity, store-and-forward delivery, and multi-guardian federation. Your messages arrive — even when traditional networks fail.
Core Capabilities
Enterprise-grade infrastructure primitives for building communication systems that survive network failures, censorship, and natural disasters.
Signed Identity
Every node identified by Ed25519 keypair with SHA-256 identity hashing. Messages are signed and verified end-to-end. No trusted third parties.
Store-and-Forward
Bundles persist with configurable TTL until the recipient reconnects. Messages are never lost, even when delivery takes days.
Multi-Guardian Federation
Nodes exchange registry hints and forward bundles across guardians automatically. No single point of failure in the network.
Privacy by Design
Region-level visibility by default. No precise geolocation exposed. Operators retain full control over what data they share.
Abuse Resilient
Built-in rate limiting, bloom-filter deduplication, bounded forwarding, and anti-loop constraints protect the network at the protocol level.
Developer SDK
An SDK covering crypto, transport, routing, incentive, storage, and more is currently in development and undergoing internal testing.
End-to-End Encryption
Full Signal Protocol stack: X3DH key agreement, Double Ratchet for forward secrecy per message, and MLS (RFC 9420) for scalable group messaging. No relay ever reads your content.
BLE Mesh Networking
Multi-hop Bluetooth Low Energy mesh with automatic fragmentation, store-and-forward offline queue, and Ed25519 challenge-response identity verification. Messages reach peers without internet.
Multi-Transport Resilience
Seven transport types — WebSocket relay, WebRTC direct, BLE mesh, Tor, LAN discovery, satellite, and sneakernet file transfer. Adaptive scoring selects the best available path.
How Messages Travel
From send to delivery, every step is authenticated, encrypted, and resilient to network interruption.
Encrypt & Sign
Client establishes a session via X3DH, encrypts each message with the Double Ratchet for forward secrecy, signs the bundle with Ed25519, and sends over any available transport.
Transport Selection
Adaptive transport scorer selects the best path: WebSocket relay, BLE mesh, WebRTC direct, Tor, or LAN. If no live path exists, the bundle queues for sneakernet or store-and-forward.
Store & Federate
Guardian stores the bundle with a configurable TTL. Federated guardians exchange bloom-filter hints and forward bundles across the network.
Privacy Protection
Optional onion routing wraps bundles in layered encryption so no relay knows both sender and recipient. Cover traffic and message mixing defeat timing correlation.
Deliver
Recipient reconnects on any transport and receives all stored bundles. Forward secrecy ensures past messages remain secure even if current keys are compromised.
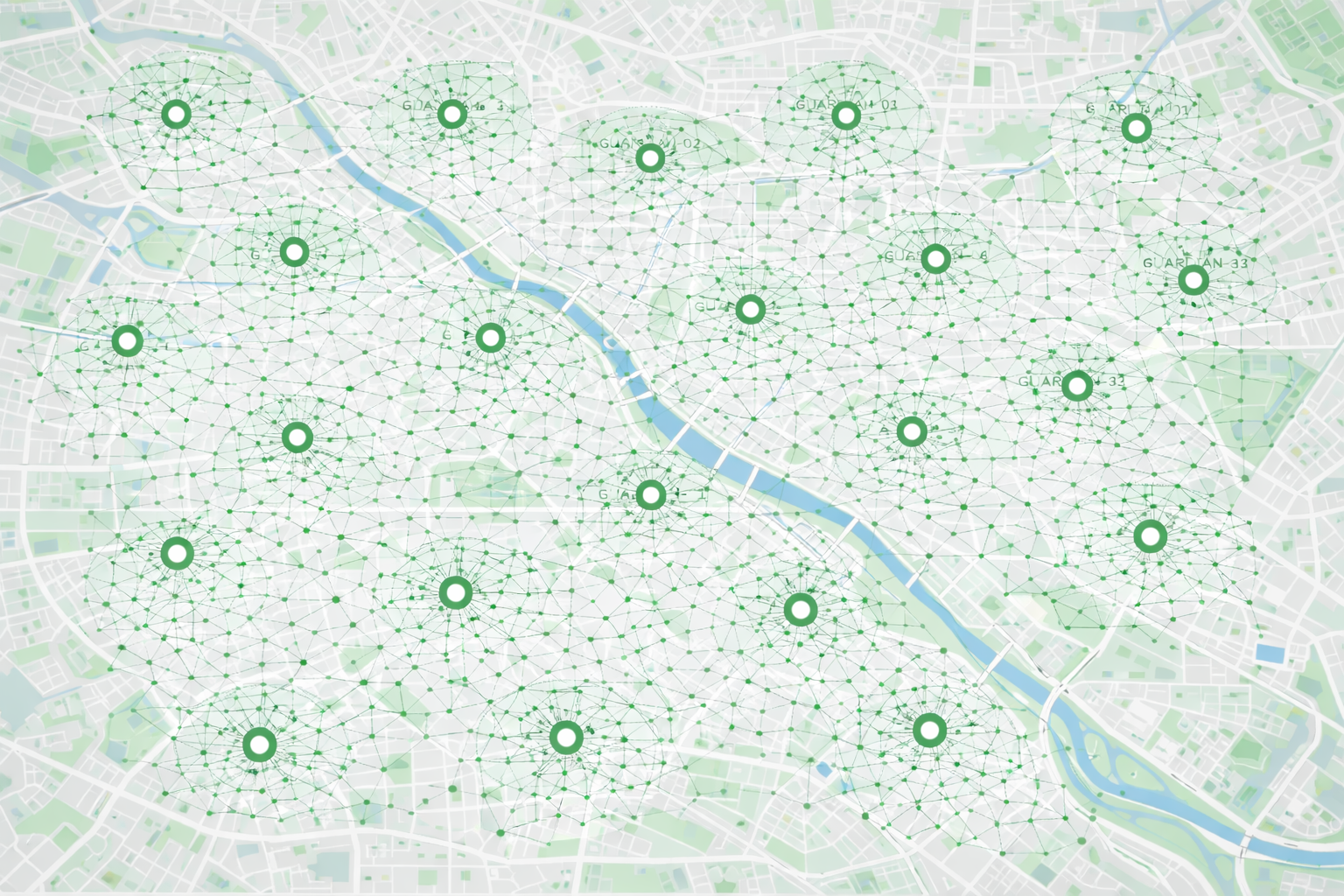
Network Status
Real-time view of the GuardianMesh relay network. All data is a privacy-safe projection at region level by default.
Built on Proven Cryptography
Every layer of the GuardianMesh protocol uses well-studied, peer-reviewed cryptographic primitives. No custom crypto. No shortcuts.
- Ed25519 signing for identity binding and message authentication
- X25519 Diffie-Hellman for authenticated key agreement
- AES-256-GCM for symmetric encryption of all payloads
- Noise XX protocol for mutually authenticated transport sessions
- MLS (RFC 9420) for scalable, secure group messaging
- X3DH key agreement for end-to-end encrypted session establishment
- Double Ratchet providing forward secrecy per message and post-compromise recovery
- Onion routing with constant-size padding (512 B–64 KB) for metadata resistance
Build on GuardianMesh
A developer SDK is currently in development and undergoing internal testing. It will cover crypto, transport, routing, storage, and more.
// SDK modules in development // crypto — AES-256-GCM, X3DH, Double Ratchet, MLS // transport — BLE mesh, WebRTC, Tor, LAN, satellite // routing — Gossip discovery, adaptive scoring, onion routing // dtn — Store-and-forward bundles, epidemic routing // identity — Ed25519 keypairs, trust chain, key rotation // storage — Distributed storage, secure deletion // incentive — Relay receipts, credit system, reputation